Nonetheless, CISOs need to keep abreast of the latest down-in-the-weeds tools and technologies that can benefit their organization’s security posture, as well as those tools that are widely available which could be misused by malicious actors to identify and exploit network security weaknesses.
In light of that fact, we recently spoke to Nabil Ouchn (
@toolswatch), the organizer of the Arsenal Tools exhibit and activities at the BlackHat Conferences in both the US and Europe since 2011, as well as being the founder of the portal
ToolsWatch.org.
ToolsWatch is a free interactive service designed to help auditors, penetration testers, and other security professionals keep their ethical hacking toolbox up to date with the latest and greatest resources.
Ouchn is an influential security expert with over 15 years experience in vulnerability management, compliance assessment and penetration testing, and Co-Founder of an innovative SaaS Multi-Engines Threats Scanning Solution.
As part of his research, Ouchn maintains several projects, including Default Password Enumeration (DPE), the open source correlated & cross-linked vulnerability database vFeed, and the Firefox Catalog of Auditing exTensions called FireCAT.
We asked Ouchn to assemble what he believed to be the top hacker tools every CISO should at least understand, if not actively encourage for integration into their own security programs.
(Part Two Here: Five More Hacker Tools Every CISO Should Understand)“Remember the paper
Improving the Security of Your Site by Breaking Into It written 20 years ago by Dan Farmer and Wietse Venema?” Ouchn asked. “It is still valid today. The best approach to mitigating the vulnerabilities and threats to an information system remains having the ability to prove that they exist.”
“The following is my list of tools every CISO should be on top of, and it was very hard to narrow it down to these few items with so many valuable tools out there,” Ouchn said. “My choices were driven by a combination of the tool’s value and their ease of use.”
Armitage
“Metasploit has become over the years the best framework to conduct penetration testing on network systems and IT infrastructure. Nevertheless, I will focus on
Armitage an open source effort to bring user-friendly interface to Metasploit,” Ouchn said.
“Armitage demonstrations are very convincing and allow you to analyze weak and vulnerable machines in a network in just a few clicks. The compromised devices are depicted with a lightning round,” Ouchn continued.
“This tool has brilliantly hidden the complexity of Metasploit (for a non-technical audience) in favor of usability
, and is a great way to demonstrate the security in depth of an IT architecture,” Ouchn said.
“In fact, the framework has several capabilities to exploit vulnerabilities in almost any type of layer to therefore infiltrate (by pivoting) systems to reach the network’s nerve center. Armitage should definitely be part of the CISO’s Arsenal and his internal Red Tiger team.”
HashCat
“There is constantly a battle between security folks and users when it comes to passwords. Although it is simple to deploy a Password Policy in a company, it’s also very difficult to justify it,” Ouchn noted.
“Because in a perfect world from users perspective, the best password would be the name of the family cat with no expiration date, and this fact applies to any system that requires authentication.”
“
HashCat has shown that the selection of a strong password must be done carefully, and this tool allows us to demonstrate the ease with which a password can be recovered,” Ouchn said.
“A CISO should certainly incorporate this password cracking tool in his arsenal because it allows to check the complexity of the company password policy. Of course, the complexity of a password is not the only criterion for a well-constructed policy, as there are a plethora of criteria: Duration, length, entropy, etc… So HashCat is a must have for any CISO.” (
See also John the Ripper).
Wifite
“You know what you have connected to when using your hardwired network, but have you ever wondered if the air is playing tricks on you? To test your WiFi security,
Wifite has the simplest way,” Ouchn says.
“The grip is instantaneous. It is written in Python and runs on all platforms. CISOs should need only to supply the WiFi interface they use and it does the job, verifying that the corporate wireless networks are configured according to the applicable Security Policy, and better yet, it can be used to identify any open and accessible network that can potentially be harmful in terms of Phishing” Ouchn continued.
“Wifite allows the discovery of all devices that have an active wireless capability enabled by default (like some printers for example). Wifite is a very simple and convincing way for a CISO to validate the security of wireless networks. (
See also AirCrack).WireShark
“Known for many years as
Ethereal,
WireShark is probably the best tool when it comes to sniffing for and collecting data over a network,” Ouchn says.
“On the one hand, WireShark has boosted its capabilities with the support of several types of networks (Ethernet, 802.11, etc.) and also in the simplicity of its use through a very friendly user interface.”
“WireShark allows a CISO to demonstrate that outdated protocols such as Telnet / FTP should be banned from a corporate network, and that sensitive information should be encrypted to avoid being captured by a malicious user,” Ouchn explained.
“Beyond the sniffing features, WireShark is also a great way to validate the network filtering policy. When placed near filtering devices, it can detect the protocols and communication flow in use. WireShark should be considered by any conscious CISO to validate the filtering policy and the need for encryption.
(See also Cain & Abel).Social Engineering Toolkit (SET)
“Those who attended
the latest demo by David Kennedy (SET lead developer and author) at the BlackHat Arsenal in Las Vegas understand the importance of such a tool” Ouchn said.
SET is a framework that helps the in creation of sophisticated technical attacks which operated using the credulity of the human. It can be used in the process of preparing a phishing attack mimicking a known website or trapping PDF files with the appropriate payload,” he continued. “The simplicity of use via an intuitive menu makes it an even more attractive tool.”
“It is the dream of every CISO to drive security awareness campaigns without ruining the security budget. With SET, the team in charge of security audits can design attacks scenarios and distribute them internally to the targeted users,” Ouchn says.
“This will confirm the users security perception within the company and validate the best Awareness Policy to deploy. The SET tool is very well maintained and is also based on a framework already mentioned above: Metasploit.”
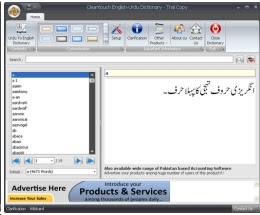
 Download an Urdu to English and English to Urdu dictionary for free, This is very interesting and easy to use dictionary you can use this dictionary for building English and Urdu vocabularies. Just write a word > enter and view the meaning of that word of English of Urdu language. You can use this dictionary at your PC and you will do not need to find the meaning on the google. This dicionary is in Rar format and you should download the 7-zip to extract the rar format files, after extracting the rar file, then click on the set up to Install this dictionary on your computer. Don't miss to download this dictionary for free.
Download an Urdu to English and English to Urdu dictionary for free, This is very interesting and easy to use dictionary you can use this dictionary for building English and Urdu vocabularies. Just write a word > enter and view the meaning of that word of English of Urdu language. You can use this dictionary at your PC and you will do not need to find the meaning on the google. This dicionary is in Rar format and you should download the 7-zip to extract the rar format files, after extracting the rar file, then click on the set up to Install this dictionary on your computer. Don't miss to download this dictionary for free.